Inadequate risk management can have serious consequences for the outcome of any IT project: In the best case scenario, the go-live is delayed; in the worst case, business continuity is jeopardized. Although every good project manager is aware of this danger, risk management is usually handled as a low priority. What is the best way to do it?

Risk management is no Rocket Science
Theoretically, every good project manager knows that projects can only be successfully completed with adequate risk management. After all, incidents are usually foreseeable and arise from known, controllable parameters – and you can only identify them if you take a close look.
In practice, the management of risk-mitigating measures is neglected or simply not carried out at all. Risk management is not an impossible task – it simply requires consistent execution.
How can risks be categorized?
To ensure that all risks are identified, I recommend categorizing them. At IN3 we use the tried-and-tested PEPT framework, which covers the following dimensions:
- People: e.g. competencies, capacities, workload, scalability, change management
- Environment: e.g. simultaneous projects and initiatives, internal and external regulation
- Processes: e.g. process completeness, process correctness, consistency, process maturity, documentation, training, testing
- Technologies: system availability and performance, connectivity, authorization, interfaces, users, etc.
How should project managers proceed?
Effective risk management can generally be divided into five successive phases. I recommend carrying out steps 1-3 as part of a workshop – preferably with an external trusted advisor who can provide a neutral perspective.
1) Risk identification
Stakeholders from all areas involved collect the risks they are aware of. A Comprehensive Risk Assembly ensures that no aspect is missing. Important: Every risk, no matter how small, should be documented. An evaluation is only carried out in the next step.
2) Risk qualification
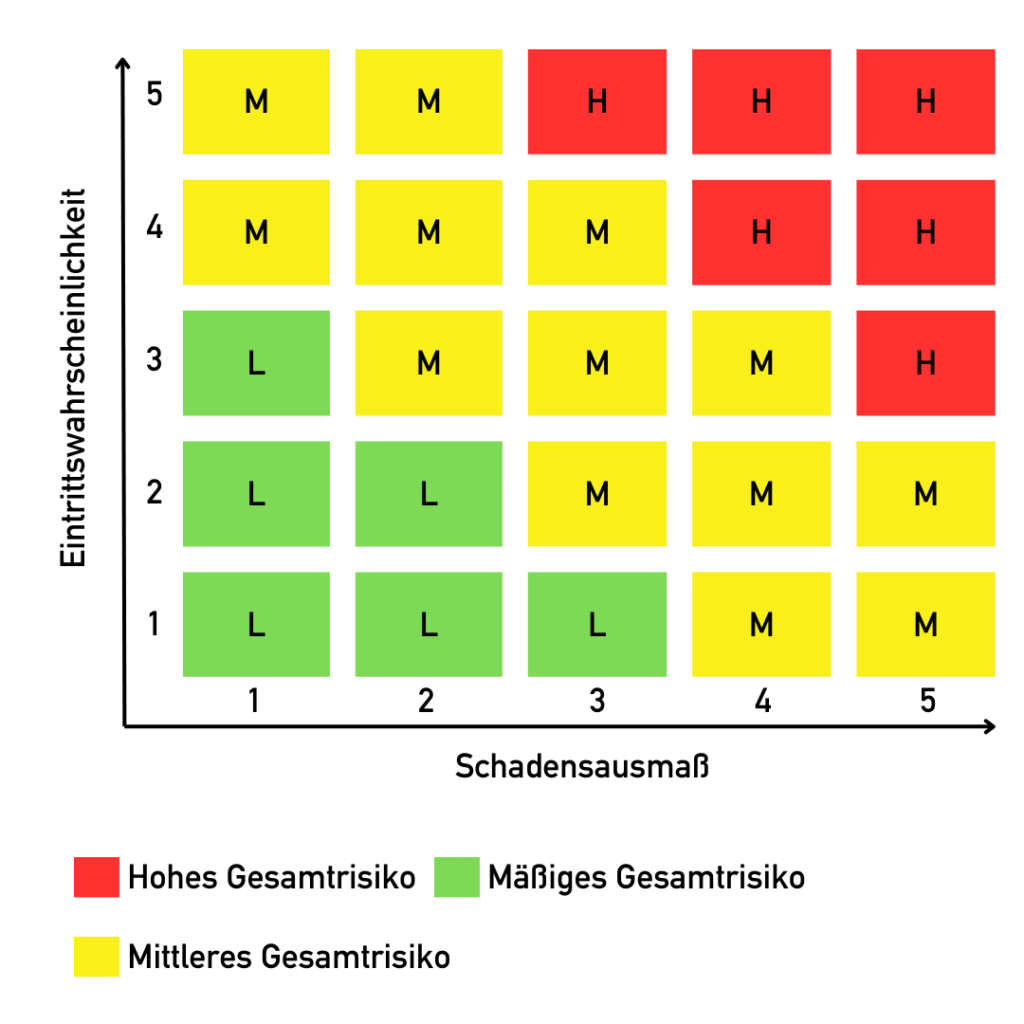
What is the hazard potential of the identified risks? And how likely are they to occur? This is what this phase is all about. A risk matrix (e.g. 5×5) is then used to qualify the risks.
3) Definition of mitigating measures
Some risks can be avoided, others cannot. In the third phase of risk management, mitigating measures are assigned to each identified risk and risk owners are appointed to ensure that those risks are effectively contained or do not arise in the first place.
4) Integration of the measures into the regular project plan (!)
During this phase, the measures are integrated into the regular project plan. Please note that risk-mitigating measures are generally not free of charge: they require resources and budget. Only by including them in the project planning you can ensure that, for example, time or capacity restrictions and dependencies are properly managed and that all team members are informed. Continuous monitoring of the measures guarantees that they are implemented effectively and adjusted if necessary.
5) Frequent reviews
In my opinion, the last step is the most important and unfortunately the most neglected. The probability and severity of risks are constantly changing! Therefore, only those who regularly carry out reviews and reassessments of risks and measures are practicing effective risk management! And more importantly, we are happy when certain risks are managed or eliminated in the course of a project. Realistically, however, new ones are added or newly identified in the course of the project. Of course, these need to be identified in the reviews.
Risk management is not a nice-to-have…
… but an absolute must-have for every IT project. I would even go so far as to say: for every business-relevant project. It ensures that all internal and external requirements are met, prepares the project team for unforeseen events and their effects and enables well-founded and effective decisions.
And believe me when I tell you: no customer has ever spent too much time on risk management. Quite the opposite.


